Minimum quality standard for cybersecurity training in healthcare
In order to combat cybersecurity attacks in healthcare centres, many organisations invest in security awareness training. However, without a shared feeling of responsibility for cyber risk mitigation throughout the organization and minimum quality standard, this training is likely to fall on deaf ears (BITSIGHT, 2020).
Therefore, in order to provide a quality assurance report for future training actions in SecureHospital.eu project (e.g. workshops, webinars and summer school) a minimum quality standard has been developed, as shown in Figure 1. In particular, the minimum quality standard depicted is based on the quality points derived in trainer interviews and workshop reports (Oomen, 2019).
Furthermore, the minimum quality standard defined below has also been suspended on already available literature and knowledge on internal stakeholder alignment (Jalali, 2018), policies & regulations (EUca, 2019; GDPR, 2019; NSP, 2019), guides (Palkmets, 2014; ENISA, 2018; Calder, 2015), frameworks (Rajamaki, 2018; Bris, 2017) and quality standards (PCISSC, 2014; NIS, 2019).
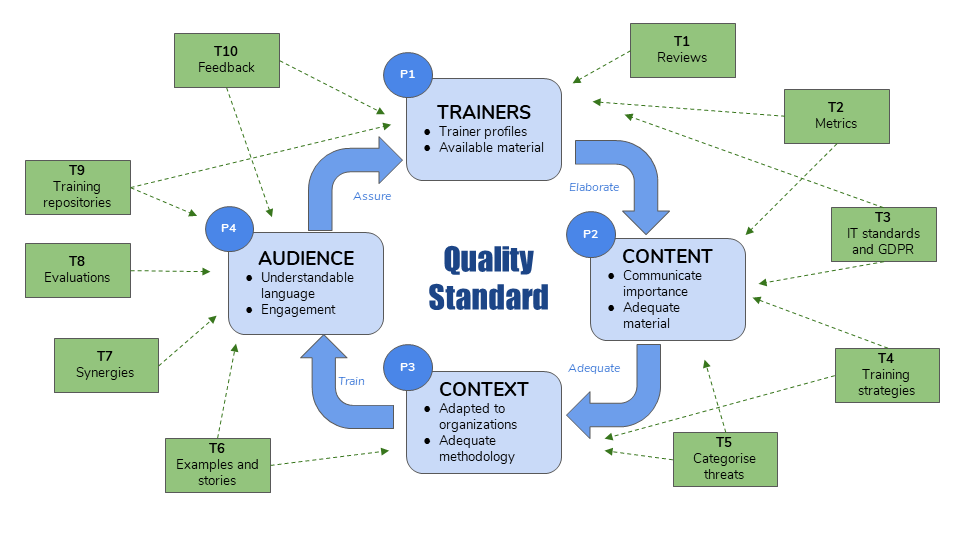
The SecureHospitals.eu minimum quality standard is composed of four points (light blue squares), nine tools (green squares) in a continuous improvement approach (indicated with blue arrows).
In particular, the main points related to the relevant minimum quality standard have the following flow (Linkedin, 2020; Quigley, 2019; Ferrell, 2018): P1) Trainers – Determine the materials and knowledge for the trainers assuming the risk of the training program, P2) Content – Decide the raw adequate material and according to the importance of communicating cybersecurity awareness, P3) Context – Check the training program fulfils the expectations and needs of the particular healthcare organization with adequate workable material and P4) Audience – Receive and respond to receivers expectation by utilising a comprehensive language and sharing common experiences relevant to the training delivered.
In addition, potential tools/techniques to be used by the trainers are indicated and pinpointed for the specific quality standard point, which they apply to. Several tools are considered (Oomen, 2019; Aumayr, 2019; PHF, 2020; Andriotis, 2019; BITSIGHT, 2020): T1) Reviews, T2) Metrics, T3) IT standards and GDPR, T4 Training strategies, T5) Categorise threats, T6) Examples and stories (story-telling), T7) Synergies, T8) Evaluations, T9) Training repositories and T10) Feedback.
Finally, the minimum quality standard points are incorporated in a continuous improvement approach (indicated with blue arrows), to effectively and efficiently increase cybersecurity awareness in healthcare centres (Drougkas, 2020).
Cybersecurity standards for healthcare
Cybersecurity standardisation is an essential component of competitiveness (EC, 2020) and it is traditionally well established in the ICT sector. International, European, National and Regionals standards are of relevance to be taken into account in training programs curricula because they were created to assemble institutions’ information-security management. Standards help also to further organise or understand data storage, security, utilization and communications best-practices in institutional practices, allowing them to analyse current vulnerabilities and tailor contemporary solutions.
Updating standards knowledge keeps an institution constantly in the know of cutting-edge cybersecurity threats and solutions. It also bolsters compliance efforts and instils an all-hands-on-deck, interdepartmental attention to preventing breaches, hacks and data loss.
The following Table 1 provides an overview of the main standards, bodies and organizations relevant to the ICT and healthcare sectors at European and International levels.
| Level | Standards/Description |
| European |
|
|
|
| International |
|
|
|
|
In general, in terms of ICT processes and recommendations the vast collection of cybersecurity standards are impulsed and discussed by several International, European and Regional level bodies, organisations, and associations (CyberWatching, 2020; Quemard, 2018; ECSO, 2017; ETSI, 2019). CEN and CENELEC EN ISO 27799:2016 standard offers guidance on information security management and information security controls in the context of the healthcare industry and medical organizations of various kinds – hospitals, labs, surgeries, medical insurers (CENEN_2020). IEC 80001-1, which deals with the application of risk management to networks incorporating medical devices, provides the roles, responsibilities and activities necessary for risk management, and is particularly relevant in the context of smart hospitals and information security (IEC, 2010). ISO also published a series of technical reports with different emphasis, which provide guidance for the implementation of IEC 80001-1. The ISO/IEC 27001 series of standards, which deals with information security management, is relevant for smart hospitals as well as for different types and sizes of organisations (ISO, 2013; ISO, 2020). CEN has an agreement for technical co-operation with ISO, while CENELEC closely cooperates with its international counterpart IEC. Also, more general for ICT standardisations is the ETSI TR 103 370 which relates to security solutions which must include a reliable and secure network infrastructure, but they must also protect the privacy of individuals and organizations (ETSI, 2019). Finally, ITU Recommendation ITU-T X.1205 provides a definition for cybersecurity for industries, such as retail banking, health care and government (ITU, 2020).
Lastly, relevant European cybersecurity agencies that should be monitored as well are ENISA and ECSO. ENISA, European Network and Information Security Agency, helps the European Commission, the Member States and the business community to address, respond and especially to prevent Network and Information Security problems. Notably it operates the EU-CERT and provides support for the ECRG, NIS activities, including harmonization of national cyber security strategies (https://www.enisa.europa.eu/). ECSO, European Cybersecurity Organization, ECSO represents an industry-led contractual counterpart to the European Commission for the implementation of the Cyber Security contractual Public-Private Partnership (cPPP). The main objective of ECSO is to support all types of initiatives or projects that aim to develop, promote, encourage European cybersecurity (http://www.ecs-org.eu/). The latter two are related to European Commission executive body, together with other entities and platforms such as NIS (https://resilience.enisa.europa.eu/nis-platform) and (http://cert.europa.eu/cert/filteredition/en/CERT-LatestNews.html) and others indicated in (ETSI, 2019).
Author
Marc Jofre
Fundacion Privada Hospital Asil de Granollers, Spain
References
Palkmets, et al., “Good Practice Guide on Training Methodologies”, ENISA (2014). https://www.enisa.europa.eu/publications/good-practice-guide-on-training-methodologies
Oomen, et al., “D4.2. Trainer interviews and workshops report”, EU H2020 SecureHospitals.eu (2019). https://project.securehospitals.eu/deliverables/
Security Awareness Program Special Interest Group PCI Security Standards Council, “Best practices for implementing a security awareness program”, PCI Data Security Standard (PCI DSS) (2014). https://www.pcisecuritystandards.org/documents/PCI_DSS_V1.0_Best_Practices_for_Implementing_Security_Awareness_Program.pdf
Rajamaki, et al., “Cybersecurity education and training in hospitals: Proactive resilience educational framework (Prosilience EF)”, IEEE Global Engineering Education Conference (EDUCON) (2018). https://ieeexplore.ieee.org/document/8363488
L. Bris, et al., “State of cybersecurity & cyber threats in healthcare organizations: Applied Cybersecurity Strategy for Managers”, Essec Business School, Harvard (2017). https://blogs.harvard.edu/cybersecurity/files/2017/01/risks-and-threats-healthcare-strategic-report.pdf
Drougkas, “PROCUREMENT GUIDELINES FOR CYBERSECURITY IN HOSPITALS” ENISA (2020). https://www.enisa.europa.eu/publications/good-practices-for-the-security-of-healthcare-services
“Cybersecurity Culture Guidelines: Behavioural Aspects of Cybersecurity”, ENISA (2018). https://www.enisa.europa.eu/publications/cybersecurity-culture-guidelines-behavioural-aspects-of-cybersecurity
“The Secret to Creating a Cyber Risk-Aware Organization”, Bitsight (2020) . https://info.bitsight.com/secret-to-creating-a-cyber-risk-aware-organization
M.S. Jalali, “Cybersecurity in Hospitals: A Systematic, Organizational Perspective”, J Med Internet Res, 20, e10059 (2018).
https://www.jmir.org/2018/5/e10059/
Become an L&D Professional”, LinkedIn (2020).
https://www.linkedin.com/learning/paths/become-an-l-d-professional-4
Calder, et al., “IT Governance – An International Guide to Data Security and ISO27001/ISO27002”, Kogan Page, Sixth Ed. (2015)
“The National Security Plan: Clarification And Examples” EU H2020 SecureHospitals.eu (2019). https://www.securehospitals.eu/the-national-security-plan-clarification-and-examples/
“General Data Protection Regulation”, EU H2020 SecureHospitals.eu (2019). https://www.securehospitals.eu/general-data-protection-regulation/
“EU Cybersecurity Act”, EU H2020 SecureHospitals.eu (2019). https://www.securehospitals.eu/eu-cybersecurity-act/
“Directive On Security Of Network And Information Systems (NIS Directive)”, EU H2020 SecureHospitals.eu (2019). https://www.securehospitals.eu/nis-directive/
“IEC 80001-1:2010 – Application of risk management for IT-networks incorporating medical devices — Part 1: Roles, responsibilities and activities”, ISO/TC 215 Health informatics (2010). https://webstore.iec.ch/publication/7482
“ISO/IEC 27001 Information Security Management”, ISO/IEC 27000 family (2013).
https://www.iso.org/isoiec-27001-information-security.html
“Evaluating Emergency Preparedness Trainings”, Public Health Foundation (PHF) (2020). http://www.phf.org/programs/preparednessresponse/evaluationrepository/Pages/Evaluating_Emergency_Preparedness_Trainings.aspx
Aumayr, et al., “D5.1. Training Strategy 1”, EU H2020 SecureHospitals.eu (2019). https://project.securehospitals.eu/deliverables/
Quigley, “ADDIE: 5 Steps To Effective Training”, Learnupon (2019). https://www.learnupon.com/blog/addie-5-steps/
Andriotis, “How to evaluate a training program: The definitive guide to techniques & tools”, Talent LMS (2019).
https://www.talentlms.com/blog/evaluate-employee-training-program/
Ferrel, et al., “Designing learning and assessment in a digital age”, Jisc (2018). https://www.jisc.ac.uk/full-guide/designing-learning-and-assessment-in-a-digital-age
“Relevant standards for cybersecurity for cybersecurity risk management”, Cyberwatching.eu EU H2020 project (2020).
https://www.cyberwatching.eu/relevant-standards-cybersecurity-risk-management
J.-P. Quemard, et al., “Guidance and gaps analysis for European standardisation Privacy standards in the information security context”, European Union Agency for Network and Information Security (ENISA) (2018).
https://www.enisa.europa.eu/publications/guidance-and-gaps-analysis-for-european-standardisation
WG1: Standardisation, certification and supply chain management, “Overview of existing Cybersecurity standards and certification schemes”, European Cyber Security Organisation (ECSO) (2017).
https://ecs-org.eu/working-groups/wg1-standardisation-certification-and-supply-chain-management
“Practical introductory guide to Technical Standards for Privacy”, European Telecommunications Standards Institute (ETSI) (2019).
https://www.etsi.org/deliver/etsi_tr/103300_103399/103370/01.01.01_60/tr_103370v010101p.pdf
“Internal Market, Industry, Entrepreneurship and SMEs”, European Commission (retrieved in 2020).
https://ec.europa.eu/growth/single-market/european-standards/ict-standardisation_en
“ISO/IEC 27000 Family”, EU H2020 SecureHospitals.eu (2020).
https://www.securehospitals.eu/iso-iec-27000-family/
“ITU-T Rec. X.1205 (04/2008) Overview of cybersecurity”, International Telecommunication Union (ITU) (2020).
https://www.itu.int/rec/dologin_pub.asp?lang=s&id=T-REC-X.1205-200804-I!!PDF-E&type=items
“CEN EN ISO 27799:2016”, European Committee for Standardisation (CEN) (2020).